If you hack the radio, can you send messages to the brakes or the steering?
And if you can, what can you do with them? That’s what two white-hat
hackers wanted to know. In their now famous
 car hack, they remotely killed the transmission of a Jeep with a Wired reporter behind the wheel. In that moment, the potential
of car hacking became real to the world.
car hack, they remotely killed the transmission of a Jeep with a Wired reporter behind the wheel. In that moment, the potential
of car hacking became real to the world.
Much has changed in the automotive industry since then, but to no one’s
surprise, security has become a top concern for automakers. New cars are
loaded with electronic controllers, computing power, lines of code and
wireless connections to the outside world. The attack surface is enormous. And
the media fallout of an attack can be detrimental to a carmaker’s
brand.
Without security, there is no safety
As we saw in the Jeep hack, once a hacker gained control of the radio, it was
easy to wreak havoc with the steering and braking systems through the in-car
network. It didn’t have a secure gateway, which acts as a firewall and
controls the handling of messages in and outside of the car. A gateway
also isolates safety-critical systems from other applications like
infotainment.
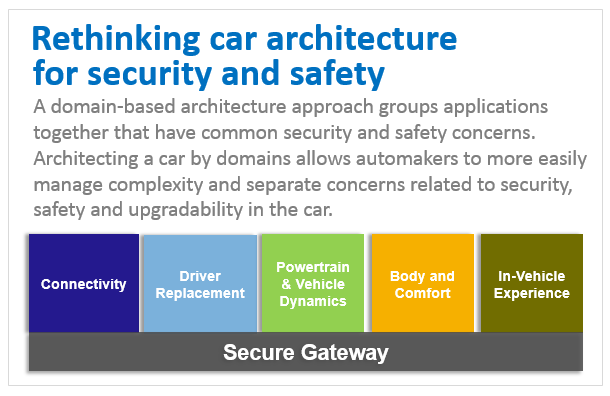
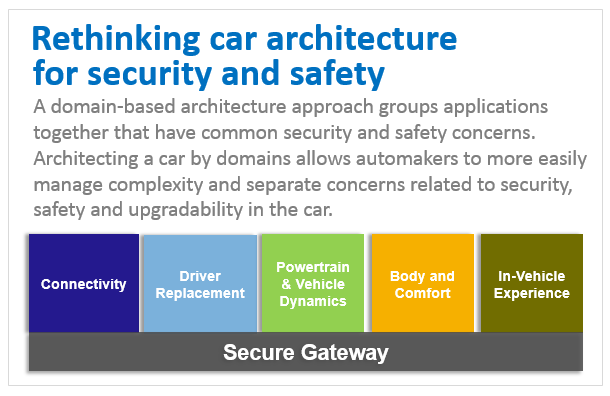
In-vehicle networks must be protected against intruders manipulating and
stealing data. This means that vehicle network architectures must be
reconsidered, separating – isolating – the various domains
inside a vehicle network.
Also, strong encryption and authentication must be used to ensure the car is
securely communicating with known and trusted entities only, as well as to
protect code and data that resides inside the vehicle network.
What other security precautions do carmakers need to make? What kind of
hardware security do automotive processors provide? These are some of the
questions and concerns we hear across the industry.
NXP first implemented hardware security on an automotive processor in 2015
Automotive processors generate, process, exchange and store massive amounts
of sensitive data —making them an attractive target for hackers. They
must have high levels of security.
As early as 2015, NXP was focused on getting security right at the processor
level. We released a dedicated automotive hardware security module (HSM) that
offered on-chip security for automotive applications, to protect software from
being manipulated and support secure software updates and data protection.
Even earlier, in 2010, we released an automotive MCU that was SHE (secure
hardware extension) compliant.
A common approach to security in our automotive platforms
Today, every new automotive processor and controller that we make includes a
dedicated hardware security module: on the S32, it’s called HSE
(Hardware Security Engine) and on the i.MX 8, it’s
called SECO (SEcure COntroller). Both modules, or engines, fully
meet the functional goals and objectives of the ‘EVITA Full’
specification and independently manage the security functions without
impacting the function of the processor or controller. Secure boot and
real-time integrity checking schemes verify that the software is authentic,
trusted and unaltered. These modules also add more flexibility to how
automakers can fix security vulnerabilities, as they enable secure
over-the-air updates that let automakers update software after the car hits
the road – without a costly recall.
Furthermore, lifecycle management mechanisms allow controlled lockdown of some
of the controller and processor features. For example, debug and serial
download are essential features during vehicle development and manufacturing
– but they’d be invaluable tools for hackers if they were
accessible on production vehicles! Lastly, there’s also built-in
hardware protection against tampering of the processor voltage, temperature
and power and hardware-enforced resource isolation.
S32 automotive platform is designed for the future growth of software,
connectivity – and security

Our new S32 automotive platform is designed for what’s coming in cars
of tomorrow – fast-to-market cars with rich in-vehicle experiences and
automated driving functions. It adds up to even more software and more
complexity. (Read more about how S32’s common architecture helps automakers
reduce software complexity across the car).
To cope with the increasing security requirements on today’s powerful
ECUs, such as secure gateways and driver assistance systems, the S32’s
embedded hardware security engine (HSE) increases the rigor of the
implementation of the cryptographic algorithms, leveraging technology and
know-how from the financial, banking and government identification industries.
i.MX 8/8X applications processor raises the bar on security for driver
information systems
Applications processors have come a long way. With roots in the earliest forms
of telematics, today’s driver information systems, including heads up
displays, digital clusters, navigation, media players and voice and data
communications, concurrently run multiple complex software stacks and require
true security. Our approach is a layered defense that comprehensively protects
the entire processing unit – from hardware and software down to the
communication links.
The i.MX 8’s secure controller (SECO) is the root-of-trust (RoT) for
the system, not only for key management, but also for authenticating,
monitoring and locking down the system controller firmware. It is also
the RoT for multiple, concurrent operating systems, from power-on to run time.
Complementing the SECO is the i.MX 8’s hardware-based tamper detection
and resistance capabilities and in-processor firewall domains that ensure data
and memory integrity of services, raising the bar on safety and security of
the driver information systems.
Security is essential – people must be able to trust their
cars
Hackers must not be able to gain control of the car or to exploit the privacy
of the driver and their data, including financial information. Automakers need
to use security solutions that will protect the electronic systems against
potential cyber attacks.
Find out more
Secure Vehicle Architecture: Multi-layer defense for connected cars
About the S32 Automotive Processing Platform
About the i.MX 8 series of Applications Processors
Cars are made of code

 car hack, they remotely
car hack, they remotely