Protecting IP Cameras: From Serious Security Risk to Trusted Asset, with One IC

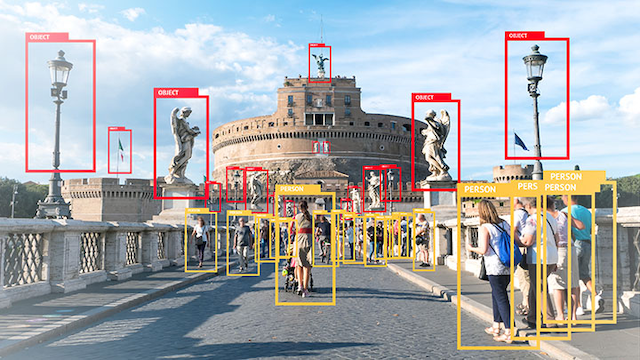
Security is always an important consideration when designing for the Internet of Things (IoT) since any connected device, small or large, is a potential entry point to a broader network. But with Internet Protocol (IP) cameras, security needs to take center stage.
Internet-connected video cameras make an ideal target for attack. They’re typically equipped with a high degree of functionality, frequently installed in unsupervised locations, and often use an always-on connection to the cloud network. It’s a combination that hackers can’t resist, and the reason why so many of the most serious distributed denial of service (DDoS) attacks, including the Mirai botnet of 2016, involved IP cameras.
Risky Business
Just about every point in an IP camera’s life cycle presents an opportunity for manipulation or theft. During installation, when the IP camera is remotely authenticated and has sent credentials for network access, hackers can steal the private information used for legitimate access. Once the camera is installed, every session with the cloud involves an authentication process that can be spoofed, and any video transmissions can be stolen or manipulated as part of a deepfake attack.
Also, manufacturers tend to use the IP camera’s connection for their own purposes, from late-stage configurations to in-field updates and periodic maintenance—and these sessions can be hijacked or abused too.
Given so many points of risk, it’s best to view security in an IP camera as a starting point for design, approaching security as a design element relevant to every aspect of functionality.
Proven Protections
There are, of course, a number of industry-proven methods for protecting IP cameras, along with security certifications that confirm the use of industry-recognized protections. If the camera connects to a Wi-Fi network, for example, it can use encryption systems, such as WPA-PSK (PBKDF2) or WPA-EAP-TLS to protect transmission. In the North American market, devices that receive FIPS 140-2 certification are verified to use proven encryption algorithms.
Whichever combination of protocols the design uses, however, it’s best practice to store and protect sensitive information, such as credentials and security keys, in silicon.
Creating the Root of Trust
Silicon-based security provides the root of trust in hardware—not software—so it's extremely difficult to tamper with or exploit.
Adding a silicon-based root of trust, in the form of a Secure Element, protects vulnerable transactions of all kinds, including device-to-device and device-to-cloud interactions in the IoT.
In an IP camera, the secure element is a platform for multiple types of protection, so the network remains safe from unauthorized access, and camera images can be trusted to be authentic and unmodified.
Tailored Protection
NXP’s EdgeLock® SE050 Secure Element is a tamper-resistant platform, designed for multiple IoT security use cases, enabling strong protection of security keys and certificates. It supports the latest TLS and WPA-EAP-TLS security protocols, as well as cryptographic functions, such as HKDF, PBKDF2 and secure SCP channel protection used with the host MCU/MPU or the cloud.
The EdgeLock SE050 saves on development time because it comes with pre-installed security code and is preconfigured with credentials—added during production or before shipment from a distributor. The preconfigured credentials provide IoT devices, like IP cameras, with a unique identity, which simplifies network onboarding and makes it more secure.
The credentials are used by the authentication process when the device connects to a Wi-Fi router and, as a result, help protect the network from unauthorized access. And, because the credentials never leave the IC, the chain of trust is preserved during the entire product lifecycle. The result is true end-to-end security built on a silicon-based a root of trust.
Four Key Operations
When designed into an IP camera, the EdgeLock SE050 protects a number of key operations: secure cloud onboarding, device-to-device authentication and attestation, late-stage parameter configuration and Wi-Fi credential protection. In addition, the EdgeLock SE050 helps to meet governmental specific security requirements, such as the FIPS standards in Canadian and US critical infrastructures. Here’s a closer look at how these features work.
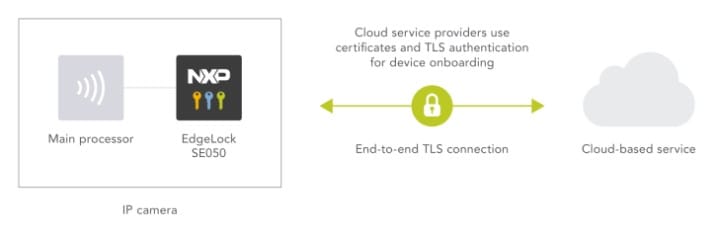
Secure Cloud Onboarding
Every connection the IP camera makes—to a public/private cloud, an edge computing platform or the infrastructure—should be a secure, zero-touch event. The EdgeLock SE050 delivers end-to-end security, from chip to edge to cloud and protects the credentials used to establish a secure TLS link with cloud service providers.
Keys are never exposed to any party during the lifetime of the device. When using TLS authentication, the EdgeLock SE050 supports TLS version 1.3 and pre-shared key cipher suites using either symmetric keys or ephemeral keys.
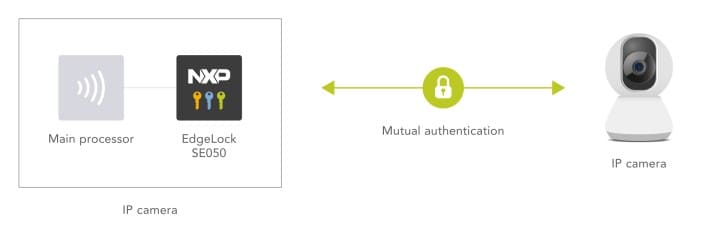
Device-to-Device Authentication and Attestation
Secure operation means using mutual authentication to prevent electronic counterfeiting and verify proof-of-origin. The term “device-to-device authentication” is a bit of a misnomer here, since the IP camera will, more typically, be connecting to gateways, data concentrators, clouds and servers, instead of other IP cameras. Either way, the EdgeLock SE050 supports the mutual authentication, backed by a secure and scalable hardware root of trust, helping to ensure that only authorized devices access the network.
When it comes to attestation, and verifying that camera data is authentic, the EdgeLock SE050 can attest data and can also be used to securely derive the encryption keys used to encrypt the data to be transmitted.
If there are doubts about originality or concerns about tampering within the supply chain, the EdgeLock SE050 can be used to provide proof of device origin. Authenticity is proven using the verification of signed random numbers, and certificates are used to bind the public key with its corresponding private-key owner. The EdgeLock SE050 also provides physical safeguards, protecting against side-channel attacks and private-key tampering.
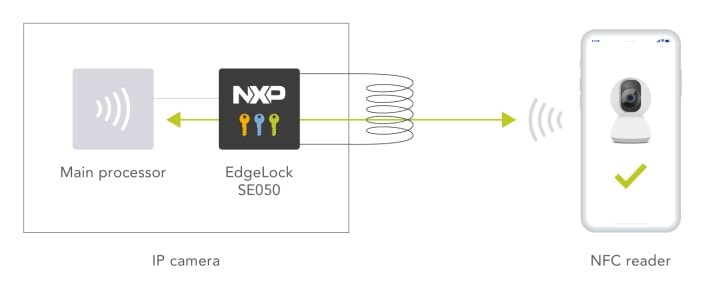
Late-Stage Parameter Configuration
Before the IP camera leaves the factory, the manufacturer may want to set configuration parameters to tailor the camera’s operation for use in a given region or use case, or by a certain customer. Ideally, the settings are modified using an NFC phone or contactless reader - a task that can be completed without having to power the camera or even take it out of its package.
To prevent unauthorized modification of parameters, EdgeLock SE05x variants integrate an ISO/IEC 14443 interface, for use with NFC. Having secured the NFC connection, the smartphone or contactless reader can safely configure the IP camera, install a specific setup or load data. The NFC reader writes information into the EdgeLock SE05x’s shared file system, the host reads this information and writes a response in the shared file system.
Wi-Fi Credential Protection
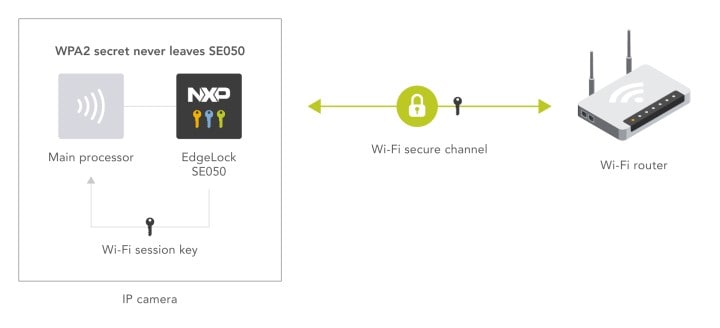
The IP camera needs secure access to a network—and in many cases—the connection will be through a WLAN or a Wi-Fi router. The EdgeLock SE050 protects the Wi-Fi credentials used to authenticate and validate devices before allowing them to use the WLAN or Wi-Fi connection. EdgeLock SE05x variants support the WPA2-PSK (PBKDF2) and WPA2-EAP-TLS security protocols, so they protect the WPA2 passphrase or secret key and generate the Wi-Fi session key used to connect to the Wi-Fi router.
Matter-Compliant Operation
For IP cameras that operate in smart home environments, the new Matter specification offers a number of benefits, from interoperability and ease of installation to high-level protection and privacy. Security is at the heart of Matter. NXP development platforms offer dedicated EdgeLock® Secure Element and secure authenticator to provide full, turnkey Matter security. These Plug and Trust security components—which can be connected to any type of processor using a standard I2C interface—take care of provisioning Matter attestation keys and certificates to the device and provide HW accelerated execution of Matter authentication protocols. With this, OEMs can simplify and accelerate manufacturing and compliance to Matter security specifications. In particular, the generation and injection of attestation and commissioning credential, as well as security logistics associated with Matter ecosystem. In addition, OEMs can further leverage the NXP EdgeLock Secure Element and secure authenticator, which are Common Criteria certified, to protect user data and user privacy, integrity of devices and secure connections to multiple clouds (including software update servers).
FIPS 140-2 Certified Security
The FIPS standards, officially known as the Federal Information Processing Standards, are developed and maintained by the National Institute of Standards and Technology (NIST) and implemented by the US government to regulate information technology and computer security. FIPS compliance is a requirement for products certified for use by government departments and agencies within the US and Canada. Also, because FIPS standards are widely recognized as being state-of-the-art, FIPS compliance is used as a purchasing guideline in the private sector, too.
Insisting on a FIPS-compliant solution gives users operating in the IoT the confidence that their setup is both interoperable and secure. For this reason, many IoT vendors, including those who aren’t working directly with the US or Canadian governments, now make it a priority to obtain FIPS compliance. They either certify the entire IoT device or, more frequently, select modules of the design. The EdgeLock SE050 offers FIPS certification as a cryptographic module. The module is a FIPS 140-2 ready-to-use certified platform with security Level 3 for the OS and app, and security Level 4 for the physical security of the hardware.
A Real-World Example
The NXP EdgeLock SE050F variant performs secure cloud onboarding and attestation in the latest multi-sensor camera from i-PRO (formerly Panasonic i-PRO Sensing Solutions), a global leader of advanced sensing technologies in the fields of intelligent surveillance, public safety and industrial/medical imaging.
The EdgeLock SE050F offers certified protection, with enhanced Common Criteria EAL 6+ and FIPS 140-2 level 3 (with security level 4 for hardware) certifications, and provides strong protection against the latest attack scenarios.
For secure cloud onboarding, the EdgeLock SE050F seamlessly connects the i-PRO camera to the cloud and then protects and encrypts data before securely transferring it over the cloud connection. For attestation, the EdgeLock SE050F verifies the integrity of the video stream, confirming that the i-PRO’s images are genuine and free of manipulation.
“The EdgeLock SE050F gave us a simple, hassle-free way to add high-level protection to our i-PRO’s new S series (standard model) and X series (eXtraordinary model) key cameras. It saved us time and effort in the design cycle, but also helped us deliver the quality and trust our customers expect from our products.”
Norio Hitsuishi, Vice President/Head of Global Security Product of i-PRO
Learn More
IP cameras may be some of the most vulnerable devices in the IoT, but adding an EdgeLock SE050 to the design can turn a device that would otherwise be a serious security risk into a trusted asset for video monitoring. Learn more about EdgeLock SE050 and its role in IoT Security. Visit i-PRO webpage to find out more on their offering.
Authors

Antje Schuetz
With more than 20 years’ experience in the semiconductors market, Antje leverages her understanding of security and mass market to drive NXP secure element solutions into the industrial and smart city markets.

Giuseppe Guagliardo
Giuseppe is product manager at NXP Semiconductors. As part of the IoT security team, he is driving NXP’s secure element offering for IoT products making security more accessible. He works with IoT and Industrial customers and supports them in understanding security threats and in the realization of their secure IoT solution. Giuseppe has experience in system engineering roles with focus on IoT, edge and cloud architectures.